| A |
Back to the menu |
| Adprep |
Extends the Active Directory® schema and updates permissions as necessary to prepare a forest and domain for a domain controller that runs a later version of the Windows Server operating system than the current domain controllers in the forest or domain. |
| Append |
Allows programs to open data files in specified directories as if they were in the current directory. If used without parameters, append displays the appended directory list. |
| Arp |
Displays and modifies entries in the Address Resolution Protocol (ARP) cache, which contains one or more tables that are used to store IP addresses and their resolved Ethernet or Token Ring physical addresses. There is a separate table for each Ethernet or Token Ring network adapter installed on your computer. Used without parameters, arp displays help. |
| Assoc |
Displays or modifies file name extension associations. If used without parameters, assoc displays a list of all the current file name extension associations. |
| At |
Schedules commands and programs to run on a computer at a specified time and date. You can use at only when the Schedule service is running. Used without parameters, at lists scheduled commands. |
| Atmadm |
Monitors connections and addresses that are registered by the ATM Call Manager on an asynchronous transfer mode (ATM) network. You can use atmadm to display statistics for incoming and outgoing calls on ATM adapters. Used without parameters, atmadm displays statistics for monitoring the status of active ATM connections |
| Attrib |
Displays, sets, or removes attributes assigned to files or directories. If used without parameters, attrib displays attributes of all files in the current directory. |
| Auditpol |
Displays information about and performs functions to manipulate audit policies. |
| Autochk |
Runs when the computer is started and prior to Windows Server® 2008 R2 starting to verify the logical integrity of a file system. |
| Autoconv |
Converts file allocation table (FAT) and FAT32 volumes to the NTFS file system, leaving existing files and directories intact at startup after Autochk runs. Volumes converted to the NTFS file system cannot be converted back to FAT or FAT32. |
| Autofmt |
Formats a drive or partition when called from the Windows Recovery Console. |
| B |
Back to the menu |
| Bcdboot |
Enables you to quickly set up a system partition, or to repair the boot environment located on the system partition. The system partition is set up by copying a simple set of Boot Configuration Data (BCD) files to an existing empty partition. |
| Bcdedit |
BCDEdit is a command-line tool for managing BCD stores. It can be used for a variety of purposes, including creating new stores, modifying existing stores, adding boot menu parameters, and so on. BCDEdit serves essentially the same purpose as Bootcfg.exe on earlier versions of Windows, but with two major improvements: Exposes a wider range of boot parameters than Bootcfg.exe and has improved scripting support. |
| Bdehdcfg |
Prepares a hard drive with the partitions necessary for BitLocker Drive Encryption. Most installations of Windows 7 will not need to use this tool because BitLocker setup includes the ability to prepare and repartition drives as required. |
| Bitsadmin |
BITSAdmin is a command-line tool that you can use to create download or upload jobs and monitor their progress. |
| Bootcfg |
Configures, queries, or changes Boot.ini file settings. |
| Break |
(Deprecated) Sets or clears extended CTRL+C checking on MS-DOS systems. If used without parameters, break displays the current setting. |
| C |
Back to the menu |
| Cacls |
Displays or modifies discretionary access control lists (DACL) on specified files. |
| Call |
Calls one batch program from another without stopping the parent batch program. The call command accepts labels as the target of the call. |
| Cd |
Displays the name of or changes the current directory. If used with only a drive letter (for example, cd C:), cd displays the names of the current directory in the specified drive. If used without parameters, cd displays the current drive and directory. (This command is the same as the chdir command.) |
| Certreq |
Certreq can be used to request certificates from a certification authority (CA), to retrieve a response to a previous request from a CA, to create a new request from an .inf file, to accept and install a response to a request, to construct a cross-certification or qualified subordination request from an existing CA certificate or request, and to sign a cross-certification or qualified subordination request. |
| Certutil |
Certutil.exe is a command-line program that is installed as part of Certificate Services. You can use Certutil.exe to dump and display certification authority (CA) configuration information, configure Certificate Services, backup and restore CA components, and verify certificates, key pairs, and certificate chains. |
| Change |
Changes Remote Desktop Session Host (RD Session Host) server settings for logons, COM port mappings, and install mode. |
| Chcp |
Changes the active console code page. If used without parameters, chcp displays the number of the active console code page. |
| Chdir |
This command is the same as the cd command. |
| Chglogon |
Enables or disables logons from client sessions on an RD Session Host server, or displays current logon status. |
| Chgport |
Lists or changes the COM port mappings to be compatible with MS-DOS applications. |
| Chgusr |
Changes the install mode for the Remote Desktop Session Host (RD Session Host) server. |
| Chkdsk |
Checks the file system and file system metadata of a volume for logical and physical errors. If used without parameters, chkdsk displays only the status of the volume and does not fix any errors. If used with the /f, /r, /x, or /b parameters, it fixes errors on the volume. |
| Chkntfs |
Displays or modifies automatic disk checking when the computer is started. If used without options, chkntfs displays the file system of the specified volume. If automatic file checking is scheduled to run, chkntfs displays whether the specified volume is dirty or is scheduled to be checked the next time the computer is started. |
| Choice |
Prompts the user to select one item from a list of single-character choices in a batch program, and then returns the index of the selected choice. If used without parameters, choice displays the default choices Y and N. |
| Cipher |
Displays or alters the encryption of directories and files on NTFS volumes. If used without parameters, cipher displays the encryption state of the current directory and any files it contains. |
| Clip |
Redirects command output from the command line to the Windows clipboard. You can then paste this text output into other programs. |
| Cls |
Clears the Command Prompt window. |
| Cluadmin |
Enables you to connect to a failover cluster (formerly known as server cluster). Used without parameters, cluadmin starts Cluster Administrator, the tool used to configure and manage failover clusters. |
| Cluster |
Creates a new cluster or configures an existing cluster. |
| Cmd |
Starts a new instance of the command interpreter, Cmd.exe. If used without parameters, cmd displays the version and copyright information of the operating system. |
| Cmdkey |
Creates, lists, and deletes stored user names and passwords or credentials. |
| Cmstp |
Installs or removes a Connection Manager service profile. Used without optional parameters, cmstp installs a service profile with default settings appropriate to the operating system and to the user’s permissions. |
| Color |
Changes the foreground and background colors in the Command Prompt window for the current session. If used without parameters, color restores the default Command Prompt window foreground and background colors. |
| Comp |
Compares the contents of two files or sets of files byte-by-byte. If used without parameters, comp prompts you to enter the files to compare. |
| Compact |
Displays or alters the compression of files or directories on NTFS partitions. If used without parameters, compact displays the compression state of the current directory and the files it contains. |
| Convert |
Converts file allocation table (FAT) and FAT32 volumes to the NTFS file system, leaving existing files and directories intact. Volumes converted to the NTFS file system cannot be converted back to FAT or FAT32. |
| Copy |
Copies one or more files from one location to another. |
| Cprofile |
Cprofile – Cprofile is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Cscript |
Starts a script so that it runs in a command-line environment. |
| Csvde |
Imports and exports data from Active Directory Domain Services (AD DS) using files that store data in the comma-separated value (CSV) format. You can also support batch operations based on the CSV file format standard. |
| D |
Back to the menu |
| Date |
Displays or sets the system date. If used without parameters, date displays the current system date setting and prompts you to enter a new date. |
| Dcdiag |
Analyzes the state of domain controllers in a forest or enterprise and reports any problems to help in troubleshooting. |
| Dcgpofix |
Recreates the default Group Policy Objects (GPOs) for a domain. |
| Dcpromo |
Installs and removes Active Directory Domain Services (AD DS). (Preferred method is Server Manager, but dcpromo should be used for RODC’s and Server core) |
| Defrag |
Locates and consolidates fragmented files on local volumes to improve system performance. |
| Del |
Deletes one or more files. This command is the same as the erase command. |
| Dfscmd |
Configures DFS folders and folder targets in a DFS namespace. |
| Dfsrmig |
The dfsrmig command migrates SYSVOL replication from File Replication Service (FRS) to Distributed File System (DFS) Replication, provides information about the progress of the migration, and modifies Active Directory Domain Services (AD DS) objects to support the migration. |
| Diantz |
This command is the same as the makecab command. |
| Dir |
Displays a list of a directory’s files and subdirectories. If used without parameters, dir displays the disk’s volume label and serial number, followed by a list of directories and files on the disk (including their names and the date and time each was last modified). For files, dir displays the name extension and the size in bytes. Dir also displays the total number of files and directories listed, their cumulative size, and the free space (in bytes) remaining on the disk. |
| Dirquota |
The dirquota command-line tool is installed with File Server Resource Manager and includes subcommands for creating and managing quotas, auto apply quotas, and quota templates, as well as configuring general administrative options for working with quotas. |
| Diskcomp |
Compares the contents of two floppy disks. If used without parameters, diskcomp uses the current drive to compare both disks. |
| Diskcopy |
Copies the contents of the floppy disk in the source drive to a formatted or unformatted floppy disk in the destination drive. If used without parameters, diskcopy uses the current drive for the source disk and the destination disk. |
| Diskedit |
diskedit has been deprecated since Windows Server 2003 – not available in Windows Server 2012 |
| DiskPart |
diskpart is a text-mode command interpreter that enables you to manage objects (disks, partitions, volumes, or virtual hard disks) by using scripts or direct input from a command prompt. |
| Diskperf |
diskperf is used to enable or disable physical and logical disk performance counters in Windows 2000 systems. |
| DiskRAID |
DiskRAID is a command-line tool that enables you to configure and manage redundant array of independent (or inexpensive) disks (RAID) storage subsystems. |
| Diskshadow |
DiskShadow is a tool that exposes the functionality offered by the Volume Shadow Copy Service (VSS). By default, DiskShadow uses an interactive command interpreter similar to that of DiskRAID or DiskPart. DiskShadow also includes a scriptable mode. |
| Dispdiag |
Logs display information to a file. |
| Djoin |
Provisions a computer account in a domain and requests an offline domain join when a computer restarts. |
| Dnscmd |
A command-line interface for managing DNS servers. This utility is useful in scripting batch files to help automate routine DNS management tasks, or to perform simple unattended setup and configuration of new DNS servers on your network. |
| Doskey |
Calls Doskey.exe (which recalls previously entered command-line commands), edits command lines, and creates macros. |
| Driverquery |
Enables an administrator to display a list of installed device drivers and their properties. If used without parameters, driverquery runs on the local computer. |
| Dsacls |
Displays and changes permissions (access control entries) in the access control list (ACL) of objects in Active Directory Domain Services (AD DS). |
| Dsadd |
Adds specific types of objects to the directory. |
| Dsamain |
Exposes Active Directory data that is stored in a snapshot or backup as a Lightweight Directory Access Protocol (LDAP) server. |
| Dsdbutil |
Performs database maintenance of the Active Directory Domain Services (AD DS) store, facilitates configuration of Active Directory Lightweight Directory Services (AD LDS) communication ports, and views AD LDS instances that are installed on a computer. |
| Dsget |
Displays the selected properties of a specific object in the directory. |
| Dsmgmt |
Facilitates managing Active Directory Lightweight Directory Services (AD LDS) application partitions, managing and controlling flexible single master operations (FSMO), and cleaning up metadata that is left behind by abandoned Active Directory domain controllers and AD LDS instances. (Abandoned domain controllers and AD LDS instances are those that are removed from the network without being uninstalled.) |
| Dsmod |
Modifies an existing object of a specific type in the directory. |
| Dsmove |
Moves a single object, within a domain, from its current location in the directory to a new location, or renames a single object without moving it in the directory tree. |
| Dsquery |
Queries the directory by using search criteria that you specify. Each of the dsquery commands finds objects of a specific object type, with the exception of dsquery *, which can query for any type of object. |
| Dsrm |
Deletes an object of a specific type or any general object from the directory. |
| E |
Back to the menu |
| Echo |
Displays messages or turns on or off the command echoing feature. If used without parameters, echo displays the current echo setting. |
| Edit |
Starts MS-DOS Editor, which creates and changes ASCII text files. |
| Endlocal |
Ends localization of environment changes in a batch file, and restores environment variables to their values before the corresponding setlocal command was run. |
| Erase |
This command is the same as the del command. See Del for syntax and parameters. |
| Eventcreate |
Enables an administrator to create a custom event in a specified event log. |
| Eventquery.vbs |
Eventquery.vbs is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Eventtriggers |
Eventtriggers is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Evntcmd |
Configures the translation of events to traps, trap destinations, or both based on information in a configuration file. |
| Exit |
Exits the Cmd.exe program (the command interpreter) or the current batch script. |
| Expand |
Expands one or more compressed files. You can use this command to retrieve compressed files from distribution disks. |
| Extract |
Extract is deprecated and is no longer part of Windows Server |
| F |
Back to the menu |
| Fc |
Compares two files or sets of files and displays the differences between them. |
| Filescrn |
The filescrn command is installed with File Server Resource Manager and includes subcommands for creating and managing file groups, file screens, file screen exceptions, and file screen templates, and for configuring general administrative options for screening files. |
| Find |
Searches for a string of text in a file or files, and displays lines of text that contain the specified string. |
| Findstr |
Searches for patterns of text in files. |
| Finger |
Displays information about a user or users on a specified remote computer (typically a computer running UNIX) that is running the Finger service or daemon. The remote computer specifies the format and output of the user information display. Used without parameters, finger displays help. |
| Flattemp |
Enables or disables flat temporary folders. |
| Fondue |
Enables Windows optional features by downloading required files from Windows Update or another source specified by Group Policy. The manifest file for the feature must already be installed in your Windows image. |
| For |
Runs a specified command for each file in a set of files. |
| Forfiles |
Selects and executes a command on a file or set of files. This command is useful for batch processing. |
| Format |
Formats a disk to accept Windows files. |
| Freedisk |
Checks to see if the specified amount of disk space is available before continuing with an installation process. |
| Fsutil |
Performs tasks that are related to file allocation table (FAT) and NTFS file systems, such as managing reparse points, managing sparse files, or dismounting a volume. If it is used without parameters, fsutil displays a list of supported subcommands. |
| Ftp |
Transfers files to and from a computer running a File Transfer Protocol (FTP) server service. Ftp can be used interactively or in batch mode by processing ASCII text files. |
| Ftype |
Displays or modifies file types that are used in file name extension associations. If used without an assignment operator (=), ftype displays the current open command string for the specified file type. If used without parameters, ftype displays the file types that have open command strings defined. |
| Fveupdate |
Fveupdate is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| G |
Back to the menu |
| Getmac |
Returns the media access control (MAC) address and list of network protocols associated with each address for all network cards in each computer, either locally or across a network. |
| Gettype |
Gettype is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Goto |
Directs cmd.exe to a labeled line in a batch program. Within a batch program, goto directs command processing to a line that is identified by a label. When the label is found, processing continues starting with the commands that begin on the next line. |
| Gpfixup |
Fix domain name dependencies in Group Policy Objects and Group Policy links after a domain rename operation. |
| Gpresult |
Displays the Resultant Set of Policy (RSoP) information for a remote user and computer. |
| Gpupdate |
Updates Group Policy settings. |
| Graftabl |
Enables Windows operating systems to display an extended character set in graphics mode. If used without parameters, graftabl displays the previous and the current code page. |
| H |
Back to the menu |
| Hashgen |
Creates or deletes BranchCache content information, also called hashes, for the content in the specified directory on a BranchCache-capable file server. |
| Help |
Provides online information about system commands (that is, non-network commands). If used without parameters, help lists and briefly describes every system command. |
| Helpctr |
Helpctr is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Hostname |
Displays the host name portion of the full computer name of the computer. |
| I |
Back to the menu |
| Icacls |
Displays or modifies discretionary access control lists (DACLs) on specified files, and applies stored DACLs to files in specified directories. |
| If |
Performs conditional processing in batch programs. |
| Inuse |
Inuse is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Ipconfig |
Displays all current TCP/IP network configuration values and refreshes Dynamic Host Configuration Protocol (DHCP) and Domain Name System (DNS) settings. Used without parameters, ipconfig displays Internet Protocol version 4 (IPv4) and IPv6 addresses, subnet mask, and default gateway for all adapters. |
| Ipxroute |
Displays and modifies information about the routing tables used by the IPX protocol. Used without parameters, ipxroute displays the default settings for packets that are sent to unknown, broadcast, and multicast addresses. |
| Irftp |
Sends files over an infrared link. |
| Ismserv |
This service enables messages to be exchanged between computers running Windows Server sites. This service is used for mail-based replication between sites. Active Directory includes support for replication between sites by using SMTP over IP transport. SMTP support is provided by the SMTP service, which is a component of IIS. The set of transports used for communication between sites must be extensible; therefore, each transport is defined in a separate add-in dynamic link library (DLL). These add-in DLLs are loaded into the ISM service, which runs on all domain controllers that are candidates for performing communication between sites. The ISM service directs send requests and receive requests to the appropriate transport add-in DLLs, which then route the messages to the ISM service on the destination computer. |
| J |
Back to the menu |
| Jetpack |
Compacts a Windows Internet Name Service (WINS) or Dynamic Host Configuration Protocol (DHCP) database. Microsoft recommends that you compact the WINS database whenever it approaches 30 MB. |
| K |
Back to the menu |
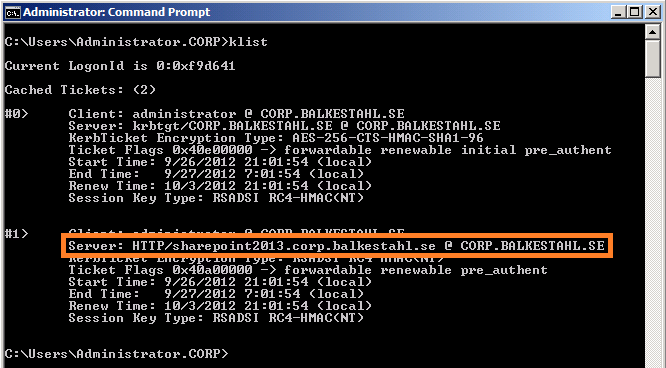
| Klist |
Displays a list of currently cached Kerberos tickets. This information applies to Windows Server 2012. |
| Ksetup |
Performs tasks that are related to setting up and maintaining Kerberos protocol and the Key Distribution Center (KDC) to support Kerberos realms, which are not also Windows domains. For examples of how this command can be used, see the Examples section in each of the related subtopics. |
| Ktmutil |
Starts the Kernel Transaction Manager utility. If used without parameters, ktmutil displays available subcommands. |
| Ktpass |
Configures the server principal name for the host or service in Active Directory Domain Services (AD DS) and generates a .keytab file that contains the shared secret key of the service. The .keytab file is based on the Massachusetts Institute of Technology (MIT) implementation of the Kerberos authentication protocol. The Ktpass command-line tool allows non-Windows services that support Kerberos authentication to use the interoperability features provided by the Kerberos Key Distribution Center (KDC) service in Windows Server 2008 R2. |
| L |
Back to the menu |
| Label |
Creates, changes, or deletes the volume label (that is, the name) of a disk. If used without parameters, the label command changes the current volume label or deletes the existing label. |
| Ldifde |
Creates, modifies, and deletes directory objects. You can also use ldifde to extend the schema, export Active Directory user and group information to other applications or services, and populate Active Directory Domain Services (AD DS) with data from other directory services. |
| Ldp |
Performs operations such as connect, bind, search, modify, add, delete against any Lightweight Directory Access Protocol (LDAP)-compatible directory, such as Active Directory Domain Services (AD DS). Ldp is an LDAP client that you use to view objects that are stored in AD DS along with their metadata, such as security descriptors and replication metadata. |
| Lodctr |
Allows you to register or save performance counter name and registry settings in a file and designate trusted services. |
| Logman |
Logman creates and manages Event Trace Session and Performance logs and supports many functions of Performance Monitor from the command line. |
| Logoff |
Logs off a user from a session on a Remote Desktop Session Host (RD Session Host) server and deletes the session from the server. |
| Lpq |
Displays the status of a print queue on a computer running Line Printer Daemon (LPD). |
| Lpr |
Sends a file to a computer or printer sharing device running the Line Printer Daemon (LPD) service in preparation for printing. |
| M |
Back to the menu |
| Macfile |
Manages File Server for Macintosh servers, volumes, directories, and files. You can automate administrative tasks by including a series of commands in batch files and starting them manually or at predetermined times. |
| Makecab |
Package existing files into a cabinet (.cab) file. |
| Manage-bde |
Used to turn on or turn off BitLocker, specify unlock mechanisms, update recovery methods, and unlock BitLocker-protected data drives. This command-line tool can be used in place of the BitLocker Drive Encryption Control Panel item. |
| mapadmin |
You can use Mapadmin to manage User Name Mapping for Microsoft Services for Network File System. |
| Md |
Creates a directory or subdirectory. This command is the same as the mkdir command. |
| Mkdir |
This command is the same as the md command. See Md for syntax and parameters. |
| Mklink |
Creates a symbolic link. |
| Mmc |
Using MMC command-line options, you can open a specific MMC console, open MMC in author mode, or specify that the 32-bit or 64-bit version of MMC is opened. |
| Mode |
Displays system status, changes system settings, or reconfigures ports or devices. If used without parameters, mode displays all the controllable attributes of the console and the available COM devices. |
| More |
Displays one screen of output at a time. |
| Mount |
You can use mount to mount Network File System (NFS) network shares. |
| Mountvol |
Creates, deletes, or lists a volume mount point. |
| Move |
Moves one or more files from one directory to another directory. |
| Mqbkup |
Backs up MSMQ message files and registry settings to a storage device and restores previously-stored messages and settings. |
| Mqsvc |
Message Queuing technology enables applications running at different times to communicate across heterogeneous networks and systems that may be temporarily offline. Message Queuing provides guaranteed message delivery, efficient routing, security, and priority-based messaging. It can be used to implement solutions for both asynchronous and synchronous messaging scenarios. |
| Mqtgsvc |
Monitors a queue for incoming messages and performs an action, in the form of an executable file or COM component, when the rules of a trigger are evaluated as true. |
| Msdt |
Invokes a troubleshooting pack at the command line or as part of an automated script, and enables additional options without user input. |
| Msg |
Sends a message to a user on a Remote Desktop Session Host (RD Session Host) server. |
| Msiexec |
Provides the means to install, modify, and perform operations on Windows Installer from the command line. |
| Msinfo32 |
Opens the System Information tool to display a comprehensive view of the hardware, system components, and software environment on the local computer. |
| Mstsc |
Creates connections to Remote Desktop Session Host (RD Session Host) servers or other remote computers, edits an existing Remote Desktop Connection (.rdp) configuration file, and migrates legacy connection files that were created with Client Connection Manager to new .rdp connection files. |
| N |
Back to the menu |
| Nbtstat |
Displays NetBIOS over TCP/IP (NetBT) protocol statistics, NetBIOS name tables for both the local computer and remote computers, and the NetBIOS name cache. Nbtstat allows a refresh of the NetBIOS name cache and the names registered with Windows Internet Name Service (WINS). Used without parameters, nbtstat displays help. |
| Net computer |
Adds or deletes a computer from a domain database. |
| Net group |
Adds, displays, or modifies global groups in domains. |
| Net localgroup |
Adds, displays, or modifies local groups. Used without parameters, net localgroup displays the name of the server and the names of local groups on the computer. |
| Net print |
Displays information about a specified printer queue or a specified print job, or controls a specified print job. |
| Net session |
Manages server computer connections. Used without parameters, net session displays information about all sessions with the local computer. |
| Net share |
Manages shared resources. Used without parameters, net share displays information about all of the resources that are shared on the local computer. For each resource, the device name(s) or pathname(s) and a descriptive comment are displayed. |
| Net use |
Connects a computer to or disconnects a computer from a shared resource, or displays information about computer connections. The command also controls persistent net connections. Used without parameters, net use retrieves a list of network connections. |
| Net user |
Adds or modifies user accounts, or displays user account information. |
| Net view |
Displays a list of domains, computers, or resources that are being shared by the specified computer. Used without parameters, net view displays a list of computers in your current domain. |
| Netcfg |
Installs the Windows Preinstallation Environment (WinPE), a lightweight version of Windows used to deploy workstations. |
| Netdiag |
The Netdiag command-line diagnostic tool helps to isolate networking and connectivity problems by performing a series of tests to determine the state of your network client. These tests and the key network status information that they expose give network administrators and support personnel a more direct means of identifying and isolating network problems. Moreover, because this tool does not require parameters or switches to be specified, support personnel and network administrators can focus on analyzing the output rather than on training users how to use the tool. |
| Netdom |
Enables administrators to manage Active Directory domains and trust relationships from the command prompt. |
| Netsh |
Netsh is a command-line scripting utility that allows you to, either locally or remotely, display or modify the network configuration of a currently running computer. |
| Netstat |
Displays active TCP connections, ports on which the computer is listening, Ethernet statistics, the IP routing table, IPv4 statistics (for the IP, ICMP, TCP, and UDP protocols), and IPv6 statistics (for the IPv6, ICMPv6, TCP over IPv6, and UDP over IPv6 protocols). Used without parameters, netstat displays active TCP connections. |
| Nfsadmin |
You can use nfsadmin to manage Server for NFS and Client for NFS. |
| Nfsshare |
You can use nfsshare to control Network File System (NFS) shares. |
| Nfsstat |
You can use nfsstat to display or reset counts of calls made to Server for NFS. |
| Nlb |
After you have installed and configured Network Load Balancing (NLB), you can control its operations and modify parameter settings using the NLB control program, nlb.exe. To simplify and centralize system administration, you can run nlb.exe either on the cluster hosts or on any remote computer running Windows Server 2008 that can access the cluster over a local or wide area network. However, certain actions, such as modifying parameters, can be performed only on the cluster hosts. |
| Nlbmgr |
Using Network Load Balancing Manager, you can configure and manage your Network Load Balancing clusters and all cluster hosts from a single computer, and you can also replicate the cluster configuration to other hosts. You can start Network Load Balancing Manager from the command-line using the command nlbmgr.exe, which is installed in the systemroot\System32 folder. |
| Nltest |
Performs network administrative tasks. |
| Nslookup |
Displays information that you can use to diagnose Domain Name System (DNS) infrastructure. Before using this tool, you should be familiar with how DNS works. The Nslookup command-line tool is available only if you have installed the TCP/IP protocol. |
| Ntbackup |
The ntbackup command is not available in Windows Vista or Windows Server 2008. Instead, you should use the wbadmin command and subcommands to back up and restore your computer and files from a command prompt. |
| Ntcmdprompt |
Runs the command interpreter Cmd.exe, rather than Command.com, after running a Terminate and Stay Resident (TSR) or after starting the command prompt from within an MS-DOS application. |
| Ntdsutil |
Ntdsutil.exe is a command-line tool that provides management facilities for Active Directory Domain Services (AD DS) and Active Directory Lightweight Directory Services (AD LDS). You can use the ntdsutil commands to perform database maintenance of AD DS, manage and control single master operations, and remove metadata left behind by domain controllers that were removed from the network without being properly uninstalled. This tool is intended for use by experienced administrators. |
| Ntfrsutl |
Dumps the internal tables, thread, and memory information for the NT File Replication Service (NTFRS). It runs against local and remote servers. The recovery setting for NTFRS in Service Control Manager (SCM) can be critical to locating and keeping important log events on the computer. This tool provides a convenient method of reviewing those settings. |
| O |
Back to the menu |
| Openfiles |
Enables an administrator to query, display, or disconnect files and directories that have been opened on a system. Also enables or disables the system Maintain Objects List global flag. |
| P |
Back to the menu |
| Pagefileconfig.vbs |
Pagefileconfig.vbs is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Path |
Sets the command path in the PATH environment variable (the set of directories used to search for executable files). If used without parameters, path displays the current command path. |
| Pathping |
Provides information about network latency and network loss at intermediate hops between a source and destination. Pathping sends multiple Echo Request messages to each router between a source and destination over a period of time and then computes results based on the packets returned from each router. Because pathping displays the degree of packet loss at any given router or link, you can determine which routers or subnets might be having network problems. Pathping performs the equivalent of the tracert command by identifying which routers are on the path. It then sends pings periodically to all of the routers over a specified time period and computes statistics based on the number returned from each. Used without parameters, pathping displays help. |
| Pause |
Suspends the processing of a batch program and displays the following prompt. |
| Pbadmin |
Pbadmin is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Pentnt |
Pentnt is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Perfmon |
Start Windows Reliability and Performance Monitor in a specific standalone mode. |
| Ping |
Verifies IP-level connectivity to another TCP/IP computer by sending Internet Control Message Protocol (ICMP) Echo Request messages. The receipt of corresponding Echo Reply messages are displayed, along with round-trip times. Ping is the primary TCP/IP command used to troubleshoot connectivity, reachability, and name resolution. Used without parameters, ping displays help. |
| Pnpunattend |
Audits a computer for device drivers, and perform unattended driver installations, or search for drivers without installing and, optionally, report the results to the command line. Use this command to specify the installation of specific drivers for specific hardware devices. |
| Pnputil |
Pnputil.exe is a command line utility that you can use to manage the driver store. You can use Pnputil to add driver packages, remove driver packages, and list driver packages that are in the store. |
| Popd |
Changes the current directory to the directory that was most recently stored by the pushd command. |
| Powercfg |
Control power settings and configure computers to default to Hibernate or Standby modes. |
| PowerShell |
Windows PowerShell™ is a task-based command-line shell and scripting language designed especially for system administration. Built on the .NET Framework, Windows PowerShell helps IT professionals and power users control and automate the administration of the Windows operating system and applications that run on Windows.The PowerShell.exe command-line tool starts a Windows PowerShell session in a Command Prompt window. When you use PowerShell.exe, you can use its optional parameters to customize the session. For example, you can start a session that uses a particular execution policy or one that excludes a Windows PowerShell profile. Otherwise, the session is the same as any session that is started in the Windows PowerShell console. |
| PowerShell_Ise |
Windows PowerShell Integrated Scripting Environment (ISE) is a graphical host application that enables you to read, write, run, debug, and test scripts and modules in a graphic-assisted environment. Key features such as IntelliSense, Show-Command, snippets, tab completion, syntax-coloring, visual debugging, and context-sensitive Help provide a rich scripting experience. |
| Print |
Sends a text file to a printer. |
| Prncnfg.vbs |
Configures or displays configuration information about a printer. |
| Prndrvr.vbs |
Adds, deletes, and lists printer drivers. |
| Prnjobs.vbs |
Pauses, resumes, cancels, and lists print jobs. |
| Prnmngr.vbs |
Adds, deletes, and lists printers or printer connections, in addition to setting and displaying the default printer. |
| Prnport.vbs |
Creates, deletes, and lists standard TCP/IP printer ports, in addition to displaying and changing port configuration. |
| Prnqctl.vbs |
Prints a test page, pauses or resumes a printer, and clears a printer queue. |
| Prompt |
Changes the Cmd.exe command prompt. If used without parameters, prompt resets the command prompt to the default setting, which is the current drive letter and directory followed by the greater than symbol (>). |
| Pubprn.vbs |
Publishes a printer to the Active Directory Domain Services. |
| Pushd |
Stores the current directory for use by the popd command, and then changes to the specified directory. |
| Pushprinterconnections |
Reads Deployed Printer Connection settings from Group Policy, and deploys/removes printer connections as needed. |
| Q |
Back to the menu |
| Qappsrv |
Displays a list of all Remote Desktop Session Host (RD Session Host) servers on the network. |
| Qprocess |
Displays information about processes that are running on a Remote Desktop Session Host (RD Session Host) server. |
| Query |
Displays information about processes, sessions, and Remote Desktop Session Host (RD Session Host) servers. |
| Quser |
Displays information about user sessions on a Remote Desktop Session Host (RD Session Host) server. |
| Qwinsta |
Displays information about sessions on a Remote Desktop Session Host (RD Session Host) server. |
| R |
Back to the menu |
| Rasdial |
Connects or disconnects a dial-up or virtual private network (VPN) connection. When you run the command without parameters, the status of current network connections is displayed. |
| Rcp |
Copies files between computers. This command has been deprecated. |
| Rd |
Deletes a directory. This command is the same as the rmdir command. |
| Rdpsign |
Enables you to digitally sign a Remote Desktop Protocol (.rdp) file. |
| Reagentc |
Configures the Windows Recovery Environment (Windows RE) and enables image recovery solutions. |
| Recover |
Recovers readable information from a bad or defective disk. |
| Redircmp |
Redirects the default container for newly created computers to a specified, target organizational unit (OU) so that newly created computer objects are created in the specific target OU instead of in CN=Computers. |
| Redirusr |
Redirects the default container for newly created users to a specified, target organizational unit (OU) so that newly created user objects are created in the specific target OU instead of in CN=Users. |
| Reg |
Performs operations on registry subkey information and values in registry entries. |
| Regini |
Modifies the registry from the command line or a script, and applies changes that were preset in one or more text files. You can create, modify, or delete registry keys, in addition to modifying the permissions on the registry keys. |
| Regsvr32 |
Registers .dll files as command components in the registry. |
| Relog |
Extracts performance counters from performance counter logs into other formats, such as text-TSV (for tab-delimited text), text-CSV (for comma-delimited text), binary-BIN, or SQL. |
| Rem |
Records comments (remarks) in a batch file or CONFIG.SYS. If no comment is specified, rem adds vertical spacing. |
| Ren |
Renames files or directories. This command is the same as the rename command. |
| Rename |
This is the same as the ren command. |
| Rendom |
Rendom.exe is a command-line tool that is used to rename Active Directory domains. A domain rename is a complex operation that also requires other tools and processes in addition to using Rendom.exe. |
| Repadmin |
Repadmin.exe helps administrators diagnose Active Directory replication problems between domain controllers running Microsoft Windows operating systems. |
| Repair-bde |
Accesses encrypted data on a severely damaged hard disk if the drive was encrypted by using BitLocker. Repair-bde can reconstruct critical parts of the drive and salvage recoverable data as long as a valid recovery password or recovery key is used to decrypt the data. |
| Replace |
Replaces files. If used with the /a option, replace adds new files to a directory instead of replacing existing files. |
| Reset session |
Enables you to reset (delete) a session on a Remote Desktop Session Host (RD Session Host) server. |
| Rexec |
Rexec is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Risetup |
The risetup command is deprecated in Windows Server® 2008 and Windows Server 2008 R2. |
| Rmdir |
This command is the same as the rd command. See Rd for syntax and parameters. |
| Robocopy |
Advanced filecopy |
| Route |
Displays and modifies the entries in the local IP routing table. |
| Rpcinfo |
Lists programs on remote computers. The rpcinfo command-line utility makes a remote procedure call (RPC) to an RPC server and reports what it finds. |
| Rpcping |
Confirms the RPC connectivity between the computer running Microsoft Exchange Server and any of the supported Microsoft Exchange Client workstations on the network. This utility can be used to check if the Microsoft Exchange Server services are responding to RPC requests from the client workstations via the network. |
| Rsh |
This command has been deprecated. Runs commands on remote computers running the RSH service or daemon. |
| Rsm |
Manages media resources using Removable Storage. Using the rsm command, you can run batch scripts for applications that do not currently support the Removable Storage API. |
| Rss |
Manages Remote Storage from the command line. Using the rss command, you can run batch scripts for applications that will allow them to access Remote Storage directly. |
| Runas |
Allows a user to run specific tools and programs with different permissions than the user’s current logon provides. |
| Rundll32 |
Loads and runs 32-bit dynamic-link libraries (DLLs). There are no configurable settings for Rundll32. |
| Rwinsta |
Enables you to reset (delete) a session on a Remote Desktop Session Host (RD Session Host) server. |
| S |
Back to the menu |
| Sc |
Communicates with the Service Controller and installed services. The SC.exe program provides capabilities similar to those provided in Services in the Control Panel. |
| Schtasks |
Schedules commands and programs to run periodically or at a specific time. Adds and removes tasks from the schedule, starts and stops tasks on demand, and displays and changes scheduled tasks. |
| Scwcmd |
Command line-tool used to perform Security Configuration Wizard tasks. |
| Secedit |
Configures and analyzes system security by comparing your current configuration to specified security templates. |
| Serverceipoptin |
Allows you to participate in the Customer Experience Improvement Program (CEIP). |
| Servermanagercmd |
Servermanagercmd.exe has been deprecated, and is not available in Windows Server 2012. |
| Serverweroptin |
Allows you to enable error reporting. |
| Set |
Displays, sets, or removes CMD.EXE environment variables. If used without parameters, set displays the current environment variable settings. |
| Setlocal |
Starts localization of environment variables in a batch file. Localization continues until a matching endlocal command is encountered or the end of the batch file is reached. |
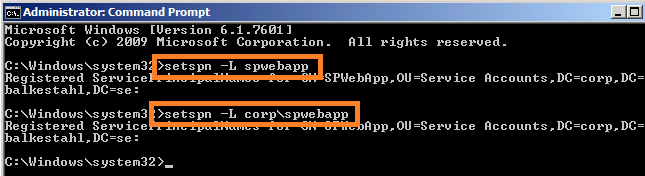
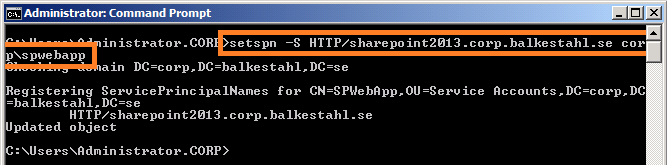
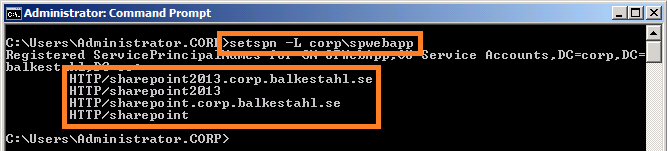
| Setspn |
Reads, modifies, and deletes the Service Principal Names (SPN) directory property for an Active Directory service account. You use SPNs to locate a target principal name for running a service. You can use setspn to view the current SPNs, reset the account’s default SPNs, and add or delete supplemental SPNs. |
| Setx |
Creates or modifies environment variables in the user or system environment, without requiring programming or scripting. The Setx command also retrieves the values of registry keys and writes them to text files. |
| Sfc |
Scans and verifies the integrity of all protected system files and replaces incorrect versions with correct versions. |
| Shadow |
Enables you to remotely control an active session of another user on a Remote Desktop Session Host (RD Session Host) server. |
| Shift |
Changes the position of batch parameters in a batch file. |
| Showmount |
You can use showmount to display mounted directories. |
| Shutdown |
Enables you to shut down or restart local or remote computers one at a time. |
| Sort |
Reads input, sorts data, and writes the results to the screen, to a file, or to another device. |
| Start |
Starts a separate Command Prompt window to run a specified program or command. |
| Storrept |
The storrept command is installed with File Server Resource Manager and includes subcommands for creating and managing storage reports and storage report tasks, as well as for configuring general administrative options for File Server Resource Manager. |
| Subst |
Associates a path with a drive letter. If used without parameters, subst displays the names of the virtual drives in effect. |
| Sxstrace |
Diagnoses side-by-side problems. |
| Sysocmgr |
Sysocmgr is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Systeminfo |
Displays detailed configuration information about a computer and its operating system, including operating system configuration, security information, product ID, and hardware properties (such as RAM, disk space, and network cards). |
| T |
Back to the menu |
| Takeown |
Enables an administrator to recover access to a file that previously was denied, by making the administrator the owner of the file. |
| Tapicfg |
Creates, removes, or displays a TAPI application directory partition, or sets a default TAPI application directory partition. TAPI 3.1 clients can use the information in this application directory partition with the directory service locator service to find and communicate with TAPI directories.You can also use Tapicfg to create or remove service connection points, which enable TAPI clients to efficiently locate TAPI application directory partitions in a domain. |
| Taskkill |
Ends one or more tasks or processes. Processes can be ended by process ID or image name. Taskkill replaces the kill tool. |
| Tasklist |
Displays a list of currently running processes on the local computer or on a remote computer. Tasklist replaces the tlist tool. |
| Tcmsetup |
Sets up or disables the TAPI client. |
| Telnet |
Communicates with a computer running the Telnet Server service. |
| Tftp |
Transfers files to and from a remote computer, typically a computer running UNIX, that is running the Trivial File Transfer Protocol (TFTP) service or daemon. |
| Time |
Displays or sets the system time. If used without parameters, time displays the current system time and prompts you to enter a new time. |
| Timeout |
Pauses the command processor for the specified number of seconds. |
| Title |
Creates a title for the Command Prompt window. |
| Tlntadmn |
Administers a local or remote computer that is running the Telnet Server Service. |
| Tracerpt |
The tracerpt command can be used to parse Event Trace Logs, log files generated by Performance Monitor, and real-time Event Trace providers. It generates dump files, report files, and report schemas. |
| Tracert |
Determines the path taken to a destination by sending Internet Control Message Protocol (ICMP) Echo Request or ICMPv6 messages to the destination with incrementally increasing Time to Live (TTL) field values. The path displayed is the list of near/side router interfaces of the routers in the path between a source host and a destination. The near/side interface is the interface of the router that is closest to the sending host in the path. |
| Tree |
Displays the directory structure of a path or of the disk in a drive graphically. |
| Tscon |
Connects to another session on a Remote Desktop Session Host (RD Session Host) server. |
| Tsdiscon |
Disconnects a session from a Remote Desktop Session Host (RD Session Host) server. |
| Tsecimp |
Imports assignment information from an Extensible Markup Language (XML) file into the TAPI server security file (Tsec.ini). You can also use this command to display the list of TAPI providers and the lines devices associated with each of them, validate the structure of the XML file without importing the contents, and check domain membership. |
| Tskill |
Ends a process running in a session on a Remote Desktop Session Host (RD Session Host) server. |
| Tsprof |
Copies the Remote Desktop Services user configuration information from one user to another. |
| Type |
Displays the contents of a text file. Use the type command to view a text file without modifying it. |
| Typeperf |
The typeperf command writes performance data to the command window or to a log file. To stop typeperf, press CTRL+C. |
| Tzutil |
Displays the Windows Time Zone Utility. |
| U |
Back to the menu |
| Uddiconfig |
Saves Universal Description, Discovery, and Integration (UDDI) configuration settings to an XML file. |
| Umount |
You can use Umount to remove Network File System (NFS)–mounted drives. |
| Unlodctr |
Removes Performance counter names and Explain text for a service or device driver from the system registry. |
| V W |
Back to the menu |
| W32tm |
You can use the W32tm.exe tool to configure Windows Time service (W32time) settings. You can also use W32tm.exe to diagnose problems with the time service. W32tm.exe is the preferred command-line tool for configuring, monitoring, or troubleshooting the Windows Time service. |
| Waitfor |
Sends or waits for a signal on a system. Waitfor is used to synchronize computers across a network. |
| Wbadmin |
Enables you to back up and restore your operating system, volumes, files, folders, and applications from a command prompt. |
| Wdsutil |
WDSUTIL is a command-line utility used for managing your Windows Deployment Services server. |
| Wecutil |
Enables you to create and manage subscriptions to events that are forwarded from remote computers, which support WS-Management protocol. |
| Ver |
Displays the operating system version number. |
| Verifier |
Driver verifier manager. |
| Verify |
Tells cmd whether to verify that your files are written correctly to a disk. If used without parameters, verify displays the current setting. |
| Wevtutil |
Enables you to retrieve information about event logs and publishers. You can also use this command to install and uninstall event manifests, to run queries, and to export, archive, and clear logs. |
| Where |
Displays the location of files that match the given search pattern. |
| Whoami |
Displays user, group and privileges information for the user who is currently logged on to the local system. If used without parameters, whoami displays the current domain and user name. |
| Winnt |
Winnt is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Winnt32 |
Winnt32 is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Winpop |
Winpop is deprecated, and is not guaranteed to be supported in future releases of Windows. |
| Winrs |
Windows Remote Management allows you to manage and execute programs remotely. |
| Winsat |
winsat assesses various features, capabilities, and attributes of a computer running Windows Vista®. |
| Wlbs |
The Wlbs command has been replaced by Nlb.exe. For more information, see Nlb |
| Wmic |
Displays WMI information inside an interactive command shell. |
| Vol |
Displays the disk volume label and serial number, if they exist. If used without parameters, vol displays information for the current drive. |
| Wscript |
Windows Script Host provides an environment in which users can execute scripts in a variety of languages, languages that use a variety of object models to perform tasks. |
| Vssadmin |
Displays current volume shadow copy backups and all installed shadow copy writers and providers. |
| X |
Back to the menu |
| Xcopy |
Copies files and directories, including subdirectories |
| Y |
Back to the menu |
| Z |
Back to the menu |

![]()