Error trying to create a new VWD hostpool in WVD v2 (spring update)
(Resolution at the end)

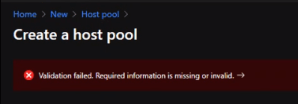
WVD spring update, create new hostpool from the Azure Portal – you fill in all the information about the setup, and when you run the validation on the last step, it fails with the shady error message:
‘Validation failed. Required information missing or invalid.’
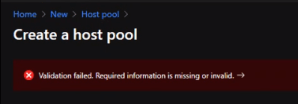
All the properties are filled in correctly, no ‘red dot’ is shown to indicate what is wrong.
The details of the error are:
ERROR TYPE
ERROR DETAILS
The template deployment failed with multiple errors. Please see details for more information.
—-
WAS THIS HELPFUL?

Well, not that helpful. In the scenario I was in when this occurred, the company had given up on the spring update due to this. No error, no indication…
The facts of the setup is, the environment where the hosts where to reside are in West Europe, and in WVD, you can only select US for the hostpool(The service/metadata), so we went with East US (Closest to Europe).
So, all hosts to be created in West Europe and Hostpool in East US (Can be any of the US options available)
Resolution:
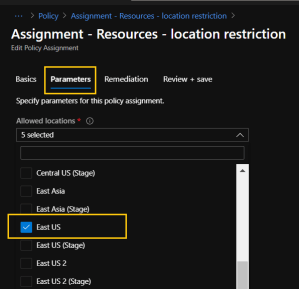
We found a similar issue after some time with Google, in that scenario, after trying a number of suggestions, the users found that they had a Azure policy attached to the subscription selected. It only allowed a few select regions, the East US was not one of them.
Same for us, when having a look at the policy on the subscription, it only had West Europe, North Europe, France and Global.
Adding East US to the allowed regions and hitting save immediately solved the problem.
Go to the subscription where you are creating your WVD hostpool, under ‘Settings’ you will find ‘Policies’

Locate a policy that has a ‘Location restriction’

Open it, click ‘Edit assignment’ at the top, then ‘Parameters’. In the dropdown, check the US region where the hostpool is to be created. Click on ‘Review + Save’ at the bottom. (This may require the owner role).
(Disclaimer – if the policy is a centralized policy, you may have to go the the owner of the policy to have it edited, like if it is applied to a management group)
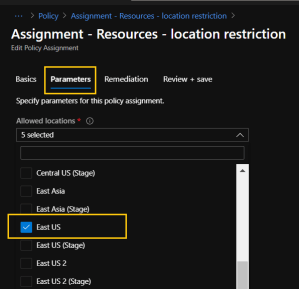
Now, you can retry the ‘Validation’ of the creating of the Hostpool. If nothing else, the policy and location restriction will not be an issue any more.
References
https://docs.microsoft.com/sv-se/azure/virtual-desktop/create-host-pools-azure-marketplace
Thanks to:

___________________________________________________________________________________________________
Enjoy!
Regards

Thomas Odell Balkeståhl on LinkedIn




![]()